“You must be logged in to do that!”
Myspace and Control
Fred Scharmen
February - May, 2006
Arch 752b: Situations, Not Plans
click here to comment
The growing popularity of social networking websites has allowed millions of people to have, for the first time, a homepage. Myspace 1 , Blogger 2 , Flickr 3 , and others have effectively lowered the barriers to entry that previously restricted web publishing. Users with no knowledge of html can create an instant and free website. Social networking sites and the communities that they enable give people the chance to construct an online identity through which they represent themselves to the community, they give people the opportunity to interact with other users that they may or may not know offline, and they provide a platform that encourages the ownership of photos, music, and other content that they can create, upload, and share. This paper will examine these three aspects of online community: identity, interaction, and ownership, in terms that are explicitly architectural; building on the metaphors of space and home that permeate the language used in and around these communities. The problems associated with self-representation, communication, and property on the web are seen as analogs of larger problems that are increasingly relevant in real life.
Nostalgia
In the mid 1990s, during the first wave of widespread internet use, the key terms used to conceptualize the network were spatial: the basic unit of the World Wide Web was the homepage, and the totality of the system itself was, at least in the media, cyberspace. Discussion of the social and political potential of online place had a flavor that was explicitly utopian and vaguely nostalgic. The personal homepage and public messageboard were seen as venues where one could be anyone that one wanted, this is the attitude parodied in the New Yorker cartoon captioned: "On the internet, nobody knows you're a dog." 4 The potential of the internet for the public realm was seen as no less fluid, the political possibilities in an alternate world free of control are best articulated by John Perry Barlow 5 in the manifesto, released in February 1996: "A Declaration of the Independence of Cyberspace" 6 . Addressed to the "Governments of the Industrial World", it begins: " Governments of the Industrial World, you weary giants of flesh and steel, I come from Cyberspace, the new home of Mind , ” and continues: "We have no elected government, nor are we likely to have one, so I address you with no greater authority than that with which liberty itself always speaks. I declare the global social space we are building to be naturally independent of the tyrannies you seek to impose on us." 7 Cyberspace was positioned as a libertarian free frontier, independent of social, political, or ideological control.
By 2006 the limitations of the spatial metaphors that had defined the internet were becoming apparent. First widespread advertising and commerce, and later, technologies like wireless networks and social software, had problematised the notion of online place. Alex Soojung-Kim Pang and David Pescovitz in the February 2006 issue of Wired Magazine wrote: “ The Internet feels less like an alternate world that we ‘go to’ and more like just another layer of life.” 8 On cyberspace, they wrote: “Clearly, we need a better word .” 9 The panel of writers and technologists that Wired assembled to find this new word (including the original popularizer of cyberspace , William Gibson) offered up infosphere, augmented reality, and ubiquitous computing 10 . Philosopher Gilles Deleuze has cited this this type of metaphorical breakdown as one symptom of a larger crisis: “We are in a generalized crisis in relation to all environments of enclosure.” 11 For Deleuze, in his essay Society of Control, the discrete spaces of enclosure, the “prison, hospital, factory, school, family” 12 are less potent as instruments of power than they had been at the height of the Industrial Revolution. Spatial enclosure embodied in architecture is giving way to the more powerful technique of access control , engendered by those same technologies that Wired identifies as composing an extra layer of daily life. John Perry Barlow’s Declaration states that in cyberspace, “Our identities have no bodies, so, unlike you, we cannot obtain order by physical coercion.” 13 This is not liberation if, as Deleuze implies, the confinement of bodies in spatial enclosure is no longer the primary means of exercising power. One does not escape the physical body into a noncorporeal cyberspace as a jailed man escapes from a prison into the wide world. If a body is recomposed as information, it is all the more subject to the specialized techniques of control: distributed surveillance, data aggregation, and the continuous modulation of production and access.
Despite the recognition of the inadequacy of spatial and corporeal metaphors in providing helpful ways to discuss network technology, and the simultaneous undermining of those same metaphors at their source by cultural and technological theory, the traditional language of architecture and urbanism persists in the discussion of online life. Myspace is space. To access the main page for a user’s account, there is a button labeled “home”.
Researcher danah boyd 14 , in a talk delivered to the American Association for the Advancement of Science in February 2006, acknowledges the tension between the techniques of enclosure and control in offline space and online social networks. The talk is titled "Identity Production in a Networked Culture: Why Youth Heart MySpace" 15 . To summarize the argument presented here: offline space for teenagers, both public and private, is controlled by the presence of adults, teenagers use the online venue of Myspace for interaction and identity production in a less controlled environment: "By going virtual, digital technologies allow youth to (re)create private and public youth space while physically in controlled spaces. IM 16 serves as a private space while MySpace provides a public component." 17 The one-to-few medium of instant messaging is presented in a way that is analogous to the private space of the teenager's room "with the door closed" 18 while the one-to-many medium of the Myspace profile page (cite) is the analog of public spaces like the mall and the neighborhood. Boyd’s central thesis is that teenagers are moving to Myspace and other online communities to produce identity and interact with each other publicly and privately in a venue that is outside of the control that adults exercise in the real space of a teenager’s everyday life. I would argue that it is exactly control in the Deleuzian sense that these teenagers and other users of Myspace are submitting to.
Identity
As boyd writes, “Profiles are digital bodies, public displays of identity where people can explore impression management.”
19
Deleuze has predicted the means by which identity is modulated in a system like Myspace: “In the societies of control ... what is important is no longer either a signature or a number, but a code: the code is a password.”
20
This password is the key to the expression and modification of the user’s digital body, their profile. Myspace acknowledges the equation between identity and profile in their Terms of Service
21
, users must agree to explicitly take responsibility for anything published on their profile using their account password: “Your Membership is solely for your personal use, and you shall not authorize others to use your account, including your profile or email address. You are solely responsible for all Content published or displayed through your account, including any email messages, and for your interactions with other members.”
22
Forbidden Content, according to the Terms, includes the predictable, anything “... obscene, lewd, excessively violent, harassing, sexually explicit or otherwise objectionable ...”
23
. There are other, more unexpected things that Myspace doesn’t want users to publish: “Your MySpace.com profile may not include the following items: telephone numbers, street addresses, last names ...”
24
Although the Terms of Service forbid the use of this personal information in the construction of your online identity, this is exactly the sort of information that is being collected behind the scenes, according to the Privacy Policy: “To facilitate searching and finding friends and acquaintances on the service, MySpace.com allows users to search for other members using first and last name, email address, and schools and/or companies where users may have attended or worked.”
25
And, from the same document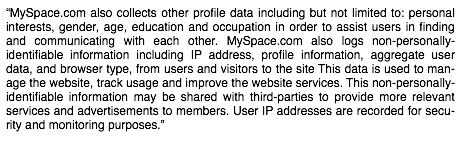 26
:
26
:
The particular reasons for this division, the embargo on the public display of personally identifiable information and the simultaneous collection of that same information privately, in aggregate form, becomes clearer when examined in terms of control: “The numerical language of control is made of codes that mark access to information, or reject it. We no longer find ourselves dealing with the mass/individual pair. Individuals have become ‘dividuals’, and masses, samples, data, markets, or ‘banks.’” 27 The data collected by Myspace is a saleable asset. In August 2005, Rupert Murdoch’s News Corporation bought Myspace’s parent company, Intermix Media, for $580 million. Typical internet business models rely on “monetizing eyeballs”: traffic can be leveraged for advertising revenue when it is assumed that everyone who visits the site will also see the ads and click on them. Myspace has, at the time of this writing in May 2006, over 75 million users 28 , and is currently the fourth most popular site on the web, with more visits than Google. There are recent signs that the long term viability of this business model may be breaking down. Google settled a class action lawsuit in March 2006 with several online retailers for $90 million. The retailers allege that Google was not doing enough to protect their advertisements against a practice known as click fraud, the fraudulent accumulation of views and clicks on ads by autonomous software agents. Internet marketing may be moving away from the practice of using clicks and views as a metric for revenue, and moving towards the collection and sale of large amounts of aggregate user data. This is perhaps the logic behind the recent acquisition, by Yahoo, of the photography sharing site Flickr and the bookmarking site del.icio.us 29 , Both of these sites have high traffic volume, but neither of them use banner ads in any significant way. They do have densely connected social networking components, and active communities. In the the Society of Control the identities of the individuals who make up these communities are transmuted into Deleuze’s ‘dividuals’ 30 , who are then aggregated into marketing databases and commodified as assets: “ Marketing has become the center or the "soul" of the corporation. We are taught that corporations have a soul, which is the most terrifying news in the world. The operation of markets is now the instrument of social control ...” 31 .
Interaction
The intended audience for the expression of identity in the digital body of the profile is the peer group of other users, as boyd writes: “Explicit reactions to their online presence offers valuable feedback. The goal is to look cool and receive peer validation.” 32 The component parts of the online soul are small pieces of marketing data. The crucial elements of the user’s profile are lists of media - favorite bands, movies, television shows, and books. Marketing also defines the terms through which users interact with members of their peer group, sharing new music, links, and video clips. Mathematician Claude Shannon, in his 1948 paper A Mathematical Theory of Communication 33 , points out that in order to establish communication, the fidelity of the communications channel must first be evaluated 34 . On the internet, the fidelity of the link between computers is tested with a signal called a ping 35 . In this type of signal, the content is unimportant, it only contains instructions for the recipient to send the message back to the sender so the transmitted copy can be compared to the original for errors. Myspace has recognized that many people stay in touch with friends through the venue of the mass email, and the developers of Myspace have constructed an analogue of this one-to-many communications medium in the form of the bulletin. Recent b ulletins from a user’s friends appear in a scrolling list on their home page . These bulletin postings are often similar in structure to chain letters, containing little more than instructions for the message to be passed on, and sometimes an implied threat or promise to ensure the instructions are carried out. More sophisticated variations on this template include a link to another interesting website, or a survey or quiz for the sender’s friends to fill out. Here the impetus for retransmission is implied by the content’s potential for enhancing the sender’s social capital. We spread these chain messages because they contain things that we think our friends might be interested in. The irrelevance of the content in the basic ping-type message: “Hey what’s up, are you still there? Are we still friends?” has been capitalized by the creators of short video clips, song downloads, and surveys. Marketers have a word for this type of content transmission: viral 36 . Viral marketing relies on the tendency of people to pass along a message if it will enhance their social capital and if they can trust its immediate source.
On my Myspace page 37 , there are 32 bulletin posts in my inbox as of this writing. 21 of those are promotional messages from friends who are in bands or who are DJs. Six of them are surveys that people have filled out and passed on for others to fill out. Two bulletin posts contain nothing more than short messages (one: “Wow, this really works!”, the other: “ HAhahaha! Frickin Great!!!”) and links . Only two out of 32 were actual personal messages. The promotional messages are, in a way, direct marketing, though they usually come from an offline involvement with the people or the music, it might be easier to think of them as opt in subscription ads that can be cancelled anytime I choose to drop the sender from my friends list. The link bulletins are basic viral marketing. In one case the link was to a company offering a tracker that would allow people who added it to their Myspace page the ability to find out who had recently viewed their profile 38 . This site hosting the tracker featured third party banner ads 39 . The other was a complicated trick to drive traffic to a site selling video clips 40 . The surveys sometimes seem like a more subtle marketing technique. Usually themed, these surveys sometime mix questions like “are you in love right now?” and “Have you bought any clothing items in the past week?” One bulletin survey, in the middle of a group of questions about sex and relationships, asked “What is your favorite Starbucks drink?” Whether these questions are about users defining their identities through the brands they buy, or whether they’re deliberately inserted by stealth marketers to raise brand awareness and collect information, the effect is the same: on Myspace, interaction between users is effectively eliminating lines between personal communication and advertising.
Ownership
The cover story of Newsweek for April 3, 2006 features the founders of photosharing site Flickr, the caption reads: “Putting the WE in Web, From Myspace to Flickr and Youtube, User Generated Sites are Rocking the Internet” 41 . In one sense, all advertising shares some characteristics that are associated with viral marketing: the content, whether it is a television show or a magazine article, is always the draw and the advertising capitalizes on the attention that the content has attracted. Just as online social networking sites have found ways to turn the users into the distributers for the advertising medium, these sites have also created their venues in such a way that the users themselves provide all of the content that draws the traffic to the site. The set of content that is monetized on Myspace includes the users identities in the form of the profile pages that they fill out, it includes the users interactions in the form of the online conversations they have with their friends and the bulletins that they send out to keep in touch, and Myspace also claims ownership of any original work that is uploaded to the site by the users.
Positive media stories about Myspace tend to focus on its potential as an alternative music distribution medium 42 , there is the option to create profiles for users bands as well as personal profiles, and Myspace provides hosting space for up to four streaming MP3s so musicians can promote their music. A reading of the Terms of Service reveals that these songs, along with any photos, writing, or any other work created and uploaded to the site, becomes the property of Myspace to use and profit from: “By posting any Content to the public areas of the Website, you hereby grant to MySpace.com the non-exclusive, fully paid, worldwide license to use, publicly perform, publicly display, modify, and translate such Content on the Website.” 43 . In November of 2005, Myspace released its first compilation album, Myspace Records Vol. 1, indicating that it intends to diversify its content distribution model beyond the internet.
Production
For Henri Lefebvre, the collapse of abstract cartesian space, the space of “common sense” 44 , reveals space as a social product. Recognition, in turn, of space as a product gives users the chance to, in a Marxist sense, seize the means of spatial production by exercising the liberatory potential of the space of differences that is left behind 45 . For Lefebvre, lived space is representational, and it is produced through the practice and discourse of its users 46 . In this sense, spatial practice is a kind of discourse, space being written into being. Space can therefore be written into being by power, but it can also be “changed and appropriated” 47 by the imagination of those who use it. When users participate in spatial production they have a chance to define their identity, and their modes of interaction and ownership on their own terms 48 .
So it is with the collapse of the abstract spatial metaphors of cyberspace and the homepage. The impossibility of realizing cyberspace’s promise of escape - from the flesh, from politics, from identity - has been foregrounded by the commodification of online space as product. Websites with more traditional business models like Salon.com, or Nytimes.com generate revenue from banner advertising, the more people there are occupying the space, the more attention or “eyeballs” are exposed to the advertising, the greater the potential revenue. In offline space, the billboard, or the corporate stadium name, are structures that serve to monetize eyeballs in the same way as traffic based banner ads. Advertising capitalizes on the surplus attention that accompanies the civic infrastructure of highways or sports arenas. Offline, the commodification of space as a product problematises the notions of civicness, or publicness that underly the supposed origins and intent of these spaces. In the 1972 case LLyod Corp. LTD. v. Tanner 49 , et al., the Supreme Court ruled that a shopping mall was not public space, and that therefore antiwar activists should have no expectation of any constitutional right to hand out leaflets protesting the draft. Justice Marshall, writing for dissent, argues in favor of the implicit publicness of the mall:
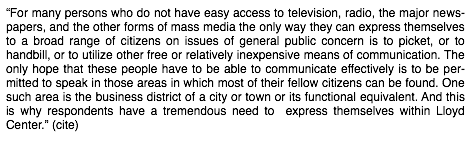
The use of the mall by antiwar protesters is, in Lefebvre’s sense, an appropriation of that space by users 50 . The transformation of the internet from utopian academic cyberspace to the monetized space of online commerce is analogous, in real life, to the transformation of the civic realm into the privately-owned-public-space of shopping. The low barriers to entry in online publishing tend to make the appropriation of online space much easier than offline. Once offline space is recognized as a social product, then there can be protest to accompany the shopping, and graffiti to accompany the billboards. Once online space becomes a user-produced social product, there can be parody and protest sites like www.walmartsucks.org 51 , and users can appropriate and remix songs, movies, and other media for themselves and their friends.
It is in the later phases of this development that control comes into play, online and off. Following Lefebvre, first, there is the collapse of unitary space, then, the commodification of space as product, next is the reappropriation of the means of spatial production by users, but finally, according to Deleuze, this process of user production itself is recuperated and monetized by the society of control. Lefebvre’s differential space is made of the remnants of abstract space’s collapse 52 , and according to Deleuze, it is precisely those continuous differences that control is uniquely suited to exploit: “Enclosures are molds, distinct castings, but controls are a modulation, like a self-deforming cast that will continuously change from one moment to the other, or like a sieve whose mesh will transmute from point to point.” 53
So it is the differences in the user’s expressions of identity that are harvested by surveillance and datamined, as control tries to discern the patterns that organize those differences as modulations, and redefine those individuals as ‘ dividuals . The offline analogue of the password is the credit card number, its links to identity take the form of buying patterns that are studied by marketers, and codes that are sought after by thieves. It is the network of connections and interactions that are traced and commodified. Offline control’s version of the billboard is the stealth marketer, the person who fakes a human interaction in order to deliver a marketing message 54 : “The disciplinary man was a discontinuous producer of energy, but the man of control is undulatory, in orbit, in a continuous network.” 55 And it is user-generated content that is monetized and resold. Copyright on artwork that would otherwise enter the public domain, like Mickey Mouse, is being extended indefinitely: “Even art has left the spaces of enclosure in order to enter into the open circuits of the bank.” 56
Media scares surrounding Myspace often center on the few horror stories of exploitation and abuse among its large teenaged user base. Writers like boyd are correct to point out that the risk of such behavior is hardly greater on Myspace than any other communications medium, and those risks are greatly outweighed by the liberatory potential inherent in introducing people to the methods of spatial production at an early age. But to return to the nostalgiac spatial metaphors of the town green, the malt shop, or the private bedroom can only help normalize the techniques of control - surveillance, shrinking commons, datamining, and stealth marketing - that are at work in those spaces. It is left as an open question whether this normalization will acclimate the users of Myspace to these specialized techniques, or if it allows them to build up a sensitivity and will to resistance that will facilitate operation in real life. As Deleuze writes: “There is no need to fear or hope, but only to look for new weapons.” 57